This is the second most important principle after Trusted Systems. Similar to Trusted Systems I'd like to emphasize the importance of the advice here.
I think every component discussed here is vital for everyone. Please consider them carefully.
I don't know what most of my passwords are, and that's just perfect. I use a password manager that auto-magically creates really good passwords, remembers them, and enters them into websites for me. Passwords like rT4&621so4@uPZ6N. I recommend this approach for every account you can use your password manager to log in to.
There are a handful of passwords you will need to manually enter. For me there are two such passwords--my Windows account login and my password manager key. I think of memorable passwords in 2 types. Ones that I have to type a lot (i.e., my Windows login) and ones I rarely have to type (i.e., my password manager).
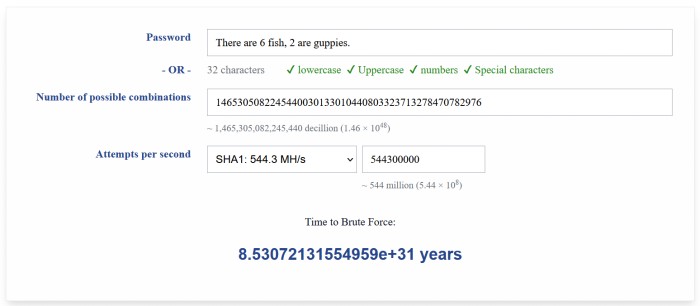
To help me remember them I usually base them on a phrase. To make them both resilient to guessing and memorable--the phrase is made up silliness but based on something real. I find the something real base gives my memory a solid anchor to re-remember what the silly phrase was. As an example, the phrase-- There are 6 fish, 2 are guppies.. This phrase is 32 characters long, includes upper case, lower case, numerics, and special characters and yet is easy for me to remember because this is based on my friend's actual fish tank. Yes, spaces count towards both password complexity and length as they must be explicitly included in any brute force attack. I might use this phrase for a password that I don't have to type that often, like my password manager. To adapt this to an often typed password I could shorten it to Ta6f, 2ag.. This password is still a little too short (I like a minimum of 12 mixed type characters) so I may add padding like "pog", Ta6f, 2ag.pog.
Proxy Nova tells me it would take "real number out of range" years to brute force the 32 character password and over 640 years to brute force the shorter one. I'm not going to make any claims about the accuracy of Proxy Nova's estimates, but I'm pretty sure it'll take a really, really long time to brute force these memorable passwords.
Your passwords need to be unique. This is why password managers are a requirement for everyone. I have over 400 passwords similar to rT4&621so4@uPZ6N in my password manager. I couldn't remember a single one of them without the manager. My manager also helps me by auditing my passwords. If I use a password on more than one account, I can see a report of my password duplications.
Unique passwords are important so that the compromise of one, remains just the one. If I reuse my password a lot and I get phished and tricked into a fake Instagram login using my main email address (happy@coolness.com) and standard password (r3alg00dp4ss). The phisher takes these credentials happy@coolness.com:r3alg00dp4ss and sprays it all over the Internet. So my bankofamerica.com, fidelity.com, citibank.com, gmail.com, netflix.com, and amazon.com are now all p'owned.
Strong, two-factor authentication ideally requires both something you know (i.e., password) and something you have (e.g., specific token or phone) to pass an authentication challenge. To prove you know what you know, you enter the password. To prove you have what you have, you enter a code from the token (hardware or software) or demonstrate possession of a specific phone by repeating back a code received on the phone.
Two-factor authentication brings a lot of security to the table. As you can imagine--the number of people that could possibly know my password has a hard limit on it. It's the number of people on this planet. On the other hand, a unique hardware/software token can be possessed only by a single person at a time. If only the person that possesses that token or phone can authenticate to the account--that reduces the field of possible attackers by more than 6 billion. It is also easily noticed if you have lost your token or phone. Not so much if someone cracked your password. Huge wins all around for Two-factor Authentication.
I use a software token on my phone and enable two-factor authentication on every account that supports it.
So.. I've got a great password AND strong authentication enabled. What could possibly go wrong? If I log in using an untrusted link--I am giving my password and token code to a bad person. Think before you authenticate. Don't use links provided by others, use your own bookmarks or type in the HTTPS address yourself.
I use a password manager and I think it would be impossible to follow authentication best practices without it. I use LastPass but there may be other, equally good offerings available.
The absolutely most important password manager feature: Security.
It is critical that even the password company cannot revert your password data file to readable, plain text. Yes, I trust LastPass to run their solution responsibly, but over the years they have been hacked more than once. My password data file is in the hands of bad people. It is easy for me to make peace with this because even if the bad guys steal every single bit of intellectual property and customer data from LastPass--they will not have my pass phrase. It will take them "real number out of range" years to decrypt my password data file. Best of luck to them.
Other important requirements: Usability.
I export my password data in plain text once or twice a year. I do this to take some of the pain out of possibility that LastPass may not be around forever. I immediately encrypt the exported data using Microsoft Excel's built-in file protection function. Microsoft Office's encryption doesn't suck anymore. For many years now they've had AES 256 as an option.
Password manager nice-to-haves:
Beating a dead horse here. This is duplication of content covered in the trusted sources and think before you authenticate discussions.
This is in the Other Tips section rather than the non-negotiables because it exceeds best-practices and the ratio of complexity to security benefit is not as compelling as the non-negotiables. I, however, am a big fan. It increases security a bit (kinda like having two passwords), and, especially when the user name must be an email address, it advances my privacy interests a lot.
It is not that changing your passwords isn't a security win. It is that if your passwords are truely unique for each account and they would take more than 100 years to brute-force compromise, the pay off just isn't that big. That--and when password rotation is forced upon us, it pushes us towards bad passwords.
The best practices today are to focus on good, unique passwords. It is only important to change a password when it may have been exposed/compromised.
